This blog is a preview of our State of Web3 Report. Sign up here to download your copy!
Any new technology that can offer benefits to the world at large likely also has the potential to be abused by bad actors for their own personal gain. Operators in the industry associated with that technology need to work to stamp out that abuse — sometimes with the help of the public sector — so that new users can feel safe adopting the technology and the industry continues to grow. If they do this successfully, we’d expect to see illicit usage of the new technology make up a smaller and smaller share of total usage over time. That positive progress is exactly what we’ve seen with cryptocurrency.
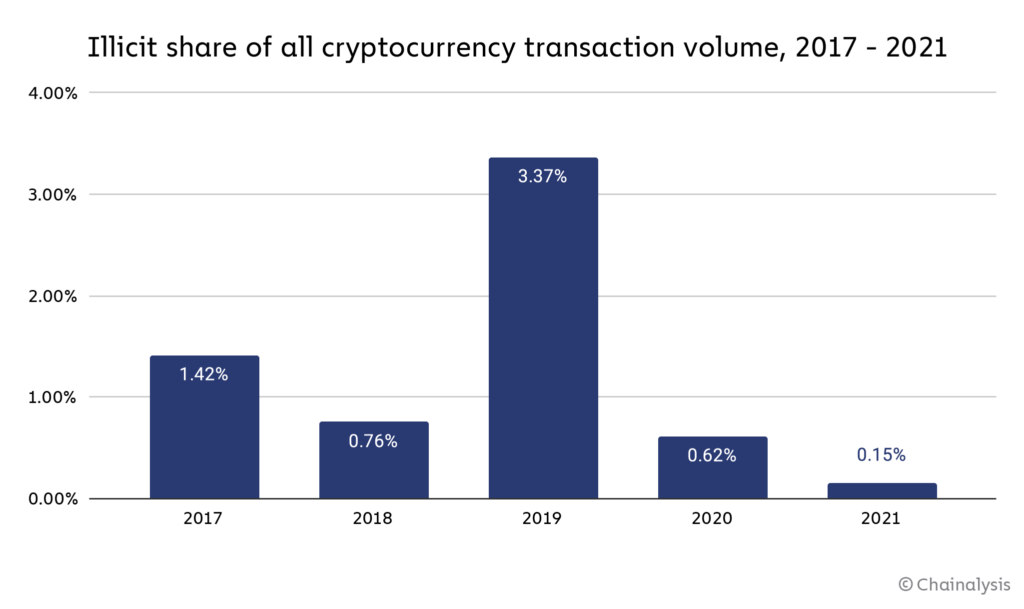
Note: 2019 has an unusually high share of illicit activity largely due to the PlusToken Ponzi scheme
While cryptocurrency-based crime remains an important problem to solve, especially given that rising overall transaction volumes mean the raw value of illicit transactions is still growing, illicit activity has become a less prominent part of the overall cryptocurrency ecosystem over the last three years.
However, DeFi specifically appears to be going through the same growing pains that cryptocurrency as a whole was previously, with illicit activity rising over the last two years.

Illicit DeFi transactions have risen steadily over the last three years, in terms of both raw value and also as a share of all transaction value. We see this primarily in two areas: Theft of funds through hacking, and abuse of DeFi protocols for money laundering. Let’s look at both in more detail below.
DeFi protocols are the go-to hacking target
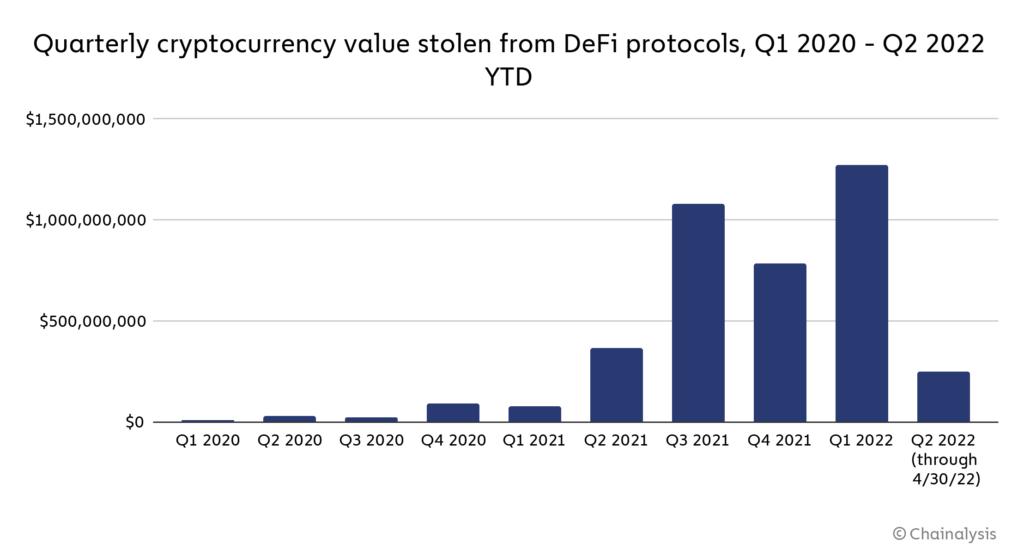
The value stolen from DeFi protocols has been trending up since the beginning of 2021, reaching its highest ever levels in Q1 2022, driven by hacks of the Ronin Bridge and Wormhole Network.
In fact, over the course of 2021, DeFi protocols became the go-to target for hackers looking to steal cryptocurrency.
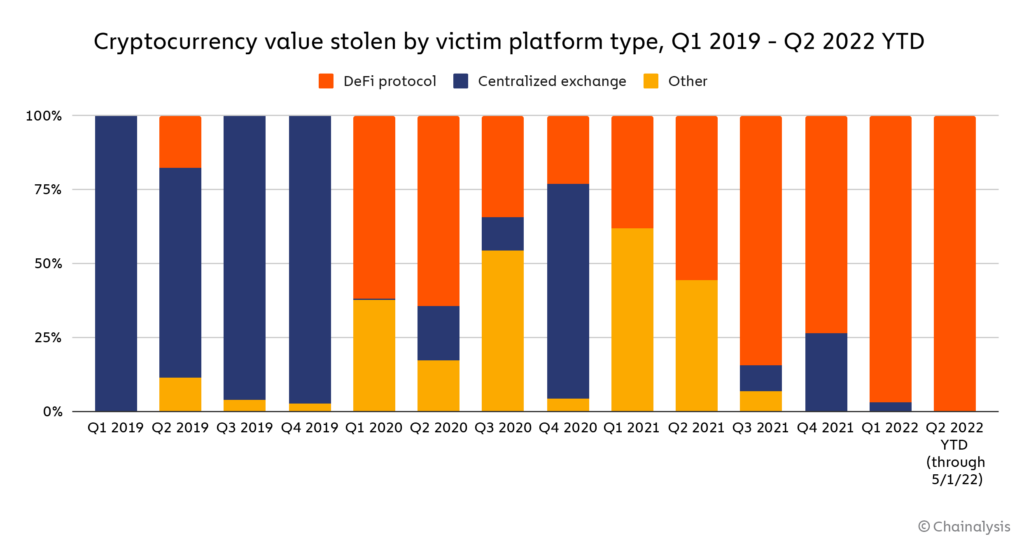
DeFi protocols have accounted for an ever-growing share of all funds stolen from cryptocurrency platforms since the beginning of 2020, and lost the vast majority of stolen funds in 2021. As of May 1, DeFi protocols account for 97% of the $1.68 billion worth of cryptocurrency stolen in 2022.
Even worse, much of the cryptocurrency stolen from DeFi protocols has gone to hacking groups associated with the North Korean government, especially in 2022.
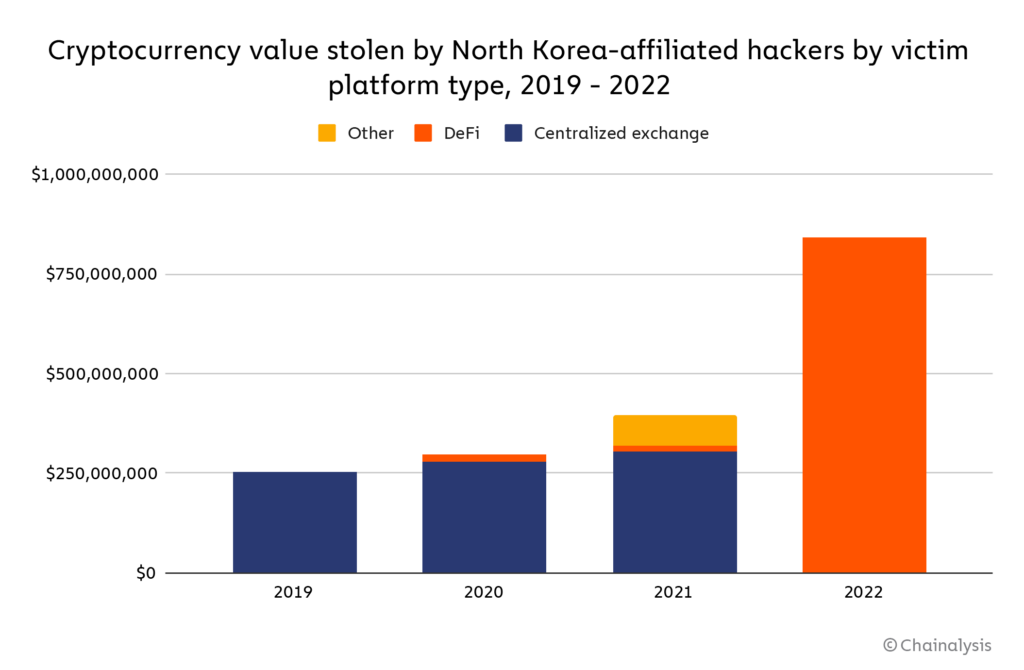
Already in 2022, North Korean hackers have had their biggest year yet for cryptocurrency theft at over $840 million, based entirely on hacks of DeFi protocols (it’s possible that North Korean hackers are responsible for other hacks, both of DeFi protocols and centralized services, that have yet to be attributed to them definitively). The data goes to show that shoring up DeFi protocols’ defenses against hackers isn’t just a matter of building trust with users so that DeFi can continue to grow. It’s also a matter of international security given that cryptocurrency stolen by North Korean hacking groups is used to support the country’s development of weapons of mass destruction. The U.S. government is taking action, and most recently sanctioned a mixer for the first time given its role in laundering funds for DPRK-linked attackers.
DeFi-based money laundering on the rise too
Money laundering is another serious issue, as DeFi protocols represent a bigger and bigger share of all funds sent from illicit addresses to services over the last two years.
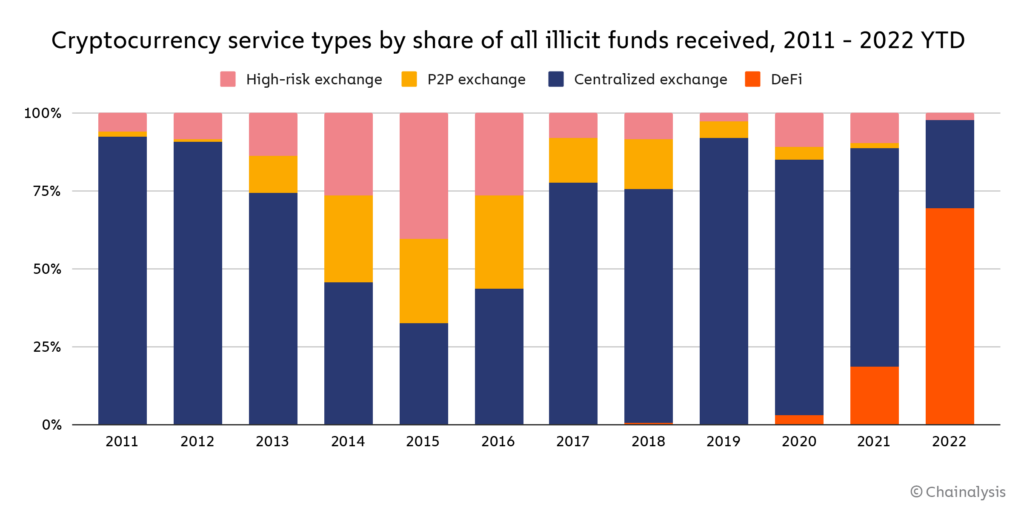
So far in 2022, DeFi protocols have become the biggest recipient of illicit funds, taking in 69% of all funds sent from addresses associated with criminal activity, compared to 19% in 2021. One reason for this is that DeFi protocols allow users to trade one type of cryptocurrency for another, which can make it more complicated to track the movement of funds — but unlike centralized services, many DeFi protocols provide this ability without taking KYC information from users, making them more attractive to criminals. Chainalysis recently added cross-chain investigations features to Reactor to address the added complexities of DeFi-enabled chain-hopping.
DeFi-based money laundering is another area where North Korean hackers are leading the way. We saw an example of this in 2021, when the infamous Lazarus Group used several DeFi protocols to launder funds after stealing more than $91 million worth of cryptocurrency from a centralized exchange.
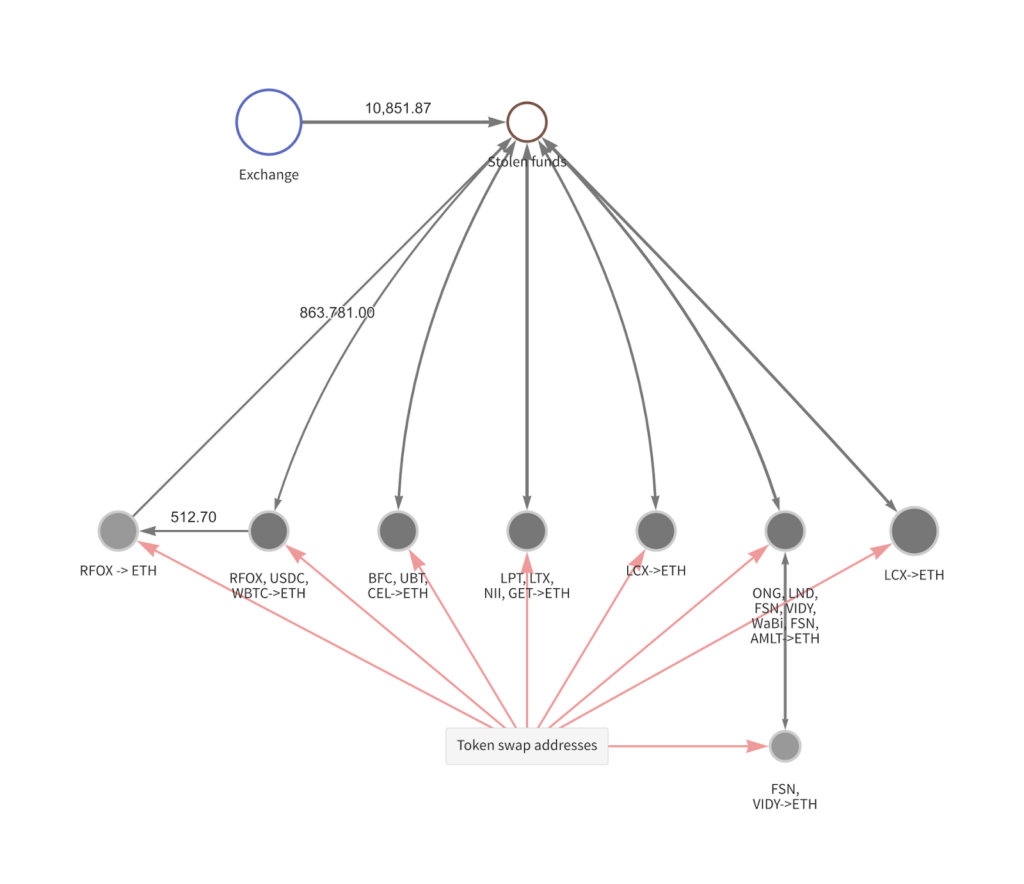
The hackers initially stole a variety of ERC-20 tokens, then used various DeFi protocols to swap those tokens for Ethereum. The hackers went on to send that Ethereum to a mixer and swap it again using DeFi protocols, this time for Bitcoin, before moving that Bitcoin to several centralized exchanges to liquidate it and receive cash. This is just one example of how hackers can abuse DeFi protocols for money laundering.
NFT wash trading lets users game the reward token system
In our 2022 Crypto Crime Report, we looked at examples of wash trading in the NFT market, and found that while most wash traders ended up losing money due to gas fees, the most successful ones turned large profits by artificially inflating their NFTs’ values and offloading them to unsuspecting users. Now, we’re going to look at another NFT wash trading scheme whose goals differ from conventional wash trading in one key way: Rather than inflating the value of any particular NFT, the goal of this scheme seems to be collecting reward tokens given out by the NFT marketplace used by the wash traders.
But before we dive in, we’ll give a quick primer on wash trading. Wash trading is a form of market manipulation in which a seller is on both sides of a trade — in other words, selling an asset to themselves — in order to create a misleading perception of that asset’s value or liquidity. Wash trading is relatively easy to do with NFTs, as some NFT trading platforms allow users to trade by simply connecting their wallet to the platform, with no need to identify themselves. One user could easily control multiple wallets and trade NFTs between them, and no one could know unless they took the time to analyze the wallets’ transaction histories.
Now, on to our example. Below, we see two wallets, which we’ve labeled Wash Trader 1 and Wash Trader 2, that have generated over 650,000 wETH in transaction volume each while selling the same three NFTs back and forth to one another.
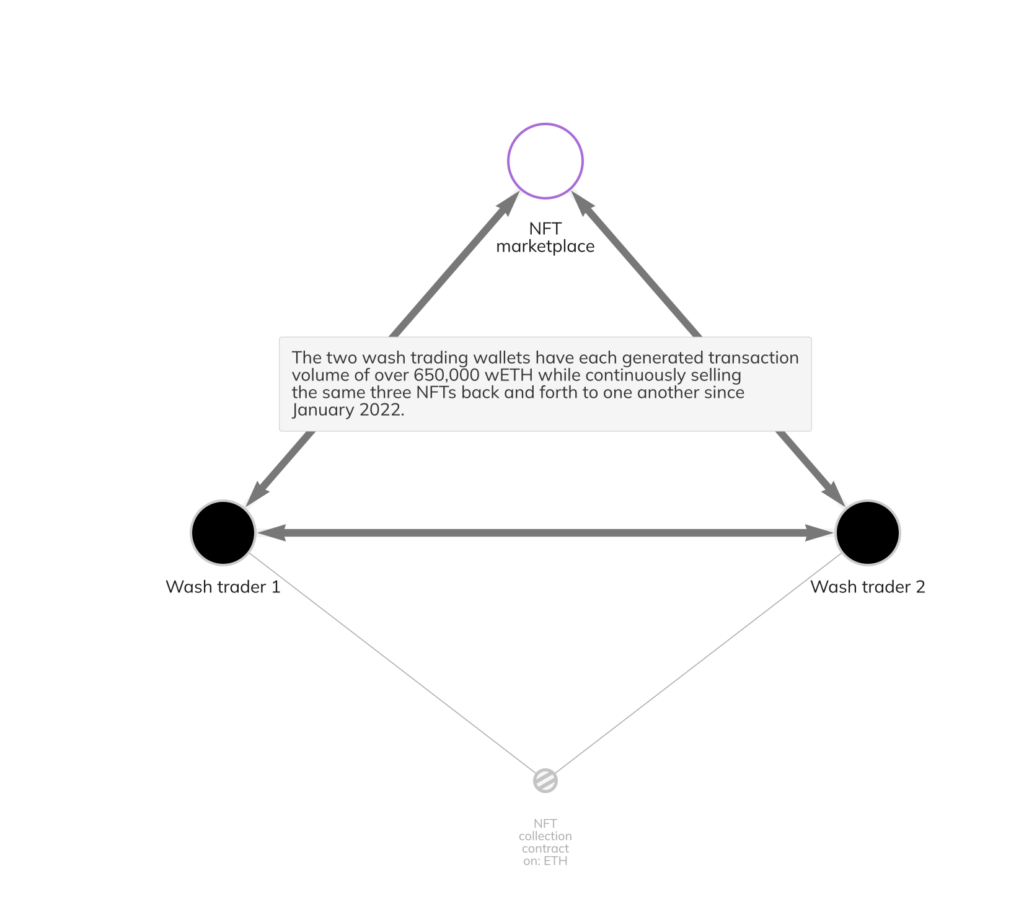
All of this activity has taken place on the same NFT marketplace. At no point has either wallet sold any of the NFTs to an outside party, so for the time being, it doesn’t appear their goal is to rip off another NFT collector by selling them an artificially inflated asset. However, this particular marketplace offers incentive rewards in the form of its own native token to users whenever they buy, sell, or trade NFTs on the platform. The two wash trader wallets have generated huge amounts of the marketplace’s rewards token through wash trading. Not only that, but the wallets have upped their earnings even more by staking their rewards tokens.
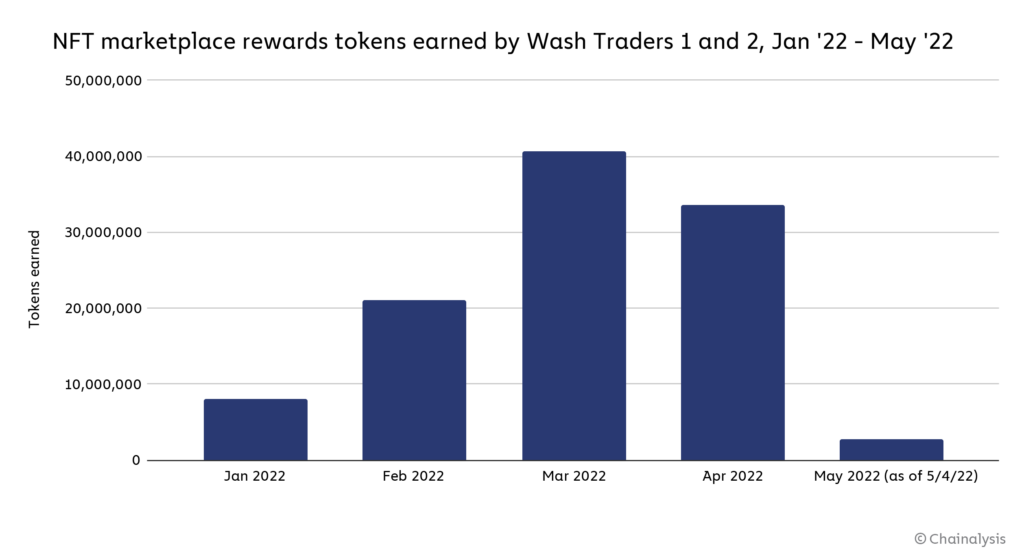
All in all, between direct earnings from platform usage and staking, the two wash trading wallets have made over 106 million rewards tokens, currently worth over $185.5 million. Gas fees on the wash trades total just $114.6 million in gas fees, giving the wash trader(s) a profit of nearly $71 million. The wallets started with initial funding of 705.6 ETH, worth $2.4 million at the time of the first transfer, making this wash trading scheme a huge success.
This type of wash trading scheme isn’t victimless. For one, the NFT marketplace is being tricked into paying out rewards for phony activity. NFT collectors throughout the market are also potentially being tricked into thinking that this NFT marketplace has more transaction activity than it really does, and the same goes for the NFT collection the wash traders are using for their transactions.
This blog is a preview of our State of Web3 Report. Sign up here to download your copy!
This website contains links to third-party sites that are not under the control of Chainalysis, Inc. or its affiliates (collectively “Chainalysis”). Access to such information does not imply association with, endorsement of, approval of, or recommendation by Chainalysis of the site or its operators, and Chainalysis is not responsible for the products, services, or other content hosted therein.
Chainalysis does not guarantee or warrant the accuracy, completeness, timeliness, suitability or validity of the information in this report and will not be responsible for any claim attributable to errors, omissions, or other inaccuracies of any part of such material.
