New updates, 1/30/23:
Last week, the Wormhole attacker converted 95,000 ETH stolen during the hack into staked ETH. The attacker then borrowed DAI using the staked ETH as collateral, and minutes later, used that borrowed DAI to purchase more staked ETH. The attacker continued this pattern to leverage borrowed capital to acquire more and more staked ETH. We can track this activity using Chainalysis Storyline, as we see below.
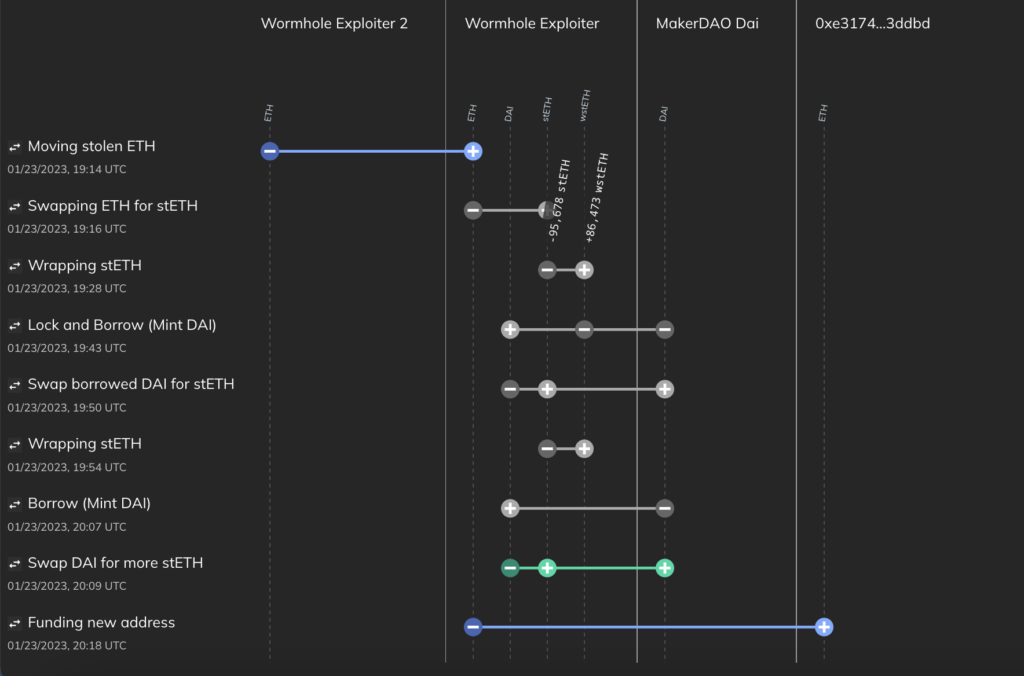
In response to these recent moves, Wormhole has reiterated its offer of a $10 million bounty in return for the attacker returning the stolen funds. We’ll continue to monitor this situation and provide updates whenever possible.
Original post: Analysis of Wormhole hack
Yesterday at around 1:30 PM ET, an unknown hacker exploited a vulnerability in the Wormhole Network, a popular cross-chain protocol, to carry out the second-largest crypto theft from a decentralized finance (DeFi) protocol ever. Across a series of transactions, the hacker made off with roughly 120,000 Wormhole Ethereum (WeETH) worth over $320 million.
With DeFi hacks, rugpulls, and thefts on the rise, this hack exemplifies the security issues that have plagued DeFi over the last year. But perhaps more importantly, it also shows how those security issues compound into threats against entire blockchains — perhaps even against the DeFi ecosystem as a whole — when cross-chain protocols are involved. Below, we’ll explain more about what made the Wormhole exploit so serious and where the funds are now.
The Wormhole Hack and Why It’s a Big Deal
Wormhole is a cross-chain bridging protocol that allows users to move cryptocurrencies and NFTs between the Solana and Ethereum blockchains. The hacker appears to have found an exploit in Wormhole’s smart contract code that allowed them to mint 120,000 Wrapped Ethereum on Solana (WeETH) without putting up the necessary equivalent Ethereum collateral.
In order to understand why this incident was more serious than the average hack, you need to know how cross-chain bridges work. Users interact with cross-chain bridges by sending funds in one asset to the bridge protocol, where those funds are then locked into the contract. The user is then issued equivalent funds of a parallel asset on the chain the protocol bridges to. In the case of Wormhole, users typically send Ether (ETH) to the protocol, where it is held as collateral, and are issued WeETH on Solana, backed by that collateral locked in the Wormhole contract on Ethereum.
Yesterday’s hack meant that $320 million worth of WeETH on Solana was unbacked for a period of time. If the WeETH wasn’t backed up with Ether, it would mean that a number of Solana-based platforms that accept WeETH as collateral could become insolvent. We could have seen users rush to sell their WeETH, causing its value to crash, which would have serious implications for the Solana blockchain and the extensive DeFi ecosystem built on top of it, as many of these protocols also rely on WeETH to back assets issued to users. And in fact, we did see a 13.5% dip in Solana’s price last night, which many attribute to concerns around the hack.
But luckily, the worst-case scenario didn’t happen. Jump Trading, Wormhole’s parent company and a major player in the Solana ecosystem, stepped up and supplied Ether to replace what was stolen, after attempts to pay the hacker a bounty in return for the stolen funds were ignored. We can see some of this on the Chainalysis Reactor graph below.
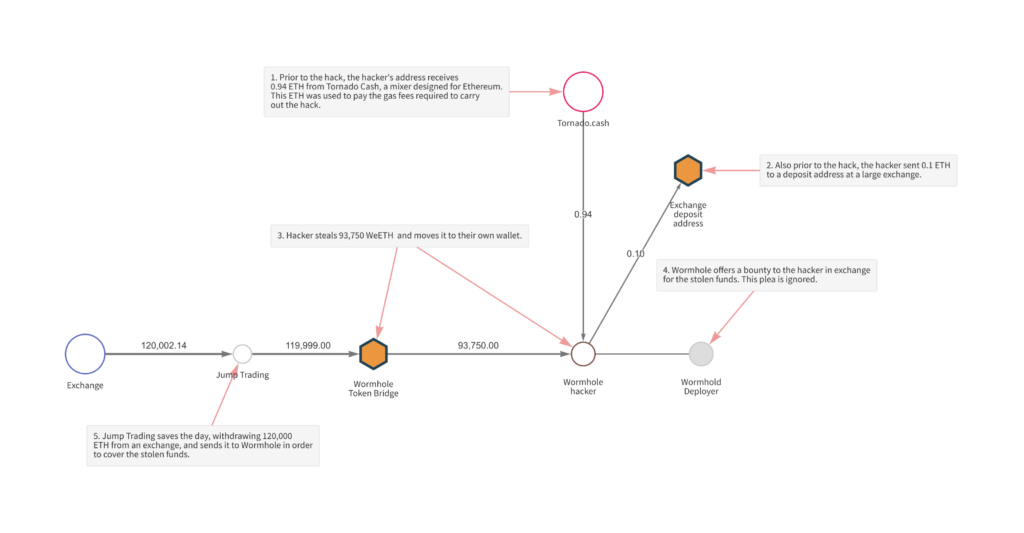
We can also see two transactions that occurred prior to the hack itself. First, the hacker received 0.94 ETH from Tornado Cash, an Ethereum-based mixer, which was used to pay for gas fees on the transactions immediately following the initial hack. Second, the hacker sent 0.1 ETH to a deposit address at a large, international exchange.
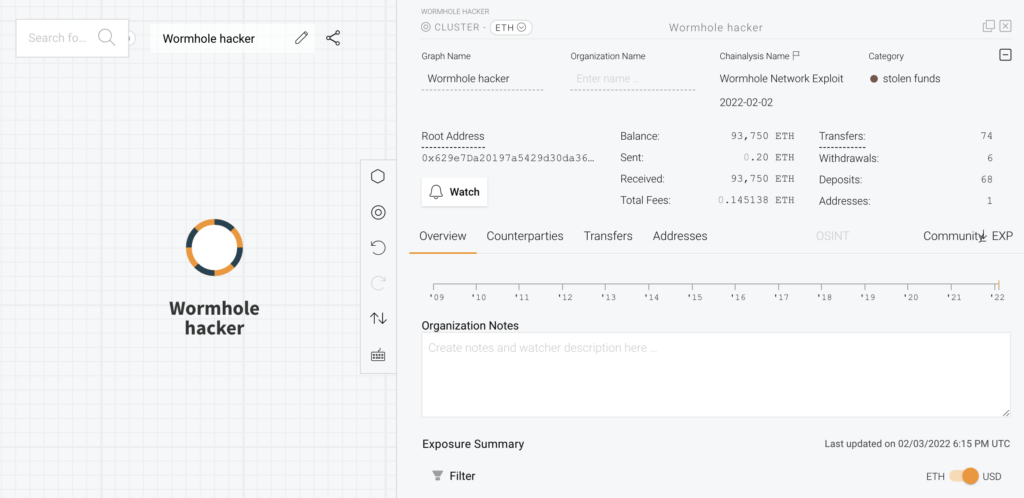
As we see from the Reactor screenshot below, the Wormhole hacker still holds 93,750 ETH on the Ethereum blockchain, which was bridged back from the Solana blockchain following the hack. We can see this Ether in the balance of the address shown on the Reactor screenshot below.
The hacker converted the remainder of the WeETH, worth roughly $42.5 million at current prices, into Solana and Wrapped Solana, with some of it first converted into Solana USDC.
The good news is that investigators, along with many in the cryptocurrency community, are closely watching this address, which will make it virtually impossible for the hacker to move the funds undetected.
Below are the crypto addresses currently holding funds stolen in the attack:
0x629e7Da20197a5429d30da36E77d06CdF796b71A
- 93,750.97 ETH
CxegPrfn2ge5dNiQberUrQJkHCcimeR4VXkeawcFBBka
- 432,662.14 SOL
Reducing risk in DeFi
As more value flows through cross-chain bridges, they become more attractive targets for hackers. The complexity of the flaw that was exploited to pull off the wormhole hack illustrates the sophistication of adversaries that smart contract developers must defend against.
DeFi protocols and cross chain bridges are now critical infrastructure in the cryptocurrency ecosystem, and successful attacks have cascading effects. If users can bridge funds across chains, it means each chain’s assets are only as secure as the other chains they connect to, along with the protocols built on top of those chains. If users think their crypto could be unbacked after a hack, we could see something akin to a bank run, creating major price declines and possibly causing protocols to become insolvent, all of which could affect the other interconnected protocols.
While not foolproof, a valuable first step towards addressing issues like this could be for extremely rigorous code audits to become the gold standard, both for developers building protocols and investors evaluating them. And over time, the strongest, safest smart contracts can serve as templates for developers to build from, such as those offered by the Open Zeppelin Project.